» Connecting VCS Providers to Terraform Cloud
Terraform Cloud is more powerful when you integrate it with your version control system (VCS) provider. Although you can use many of Terraform Cloud's features without one, a VCS connection provides additional features and improved workflows. In particular:
- When workspaces are linked to a VCS repository, Terraform Cloud can automatically initiate Terraform runs when changes are committed to the specified branch.
- Terraform Cloud makes code review easier by automatically predicting how pull requests will affect infrastructure.
- Publishing new versions of a private Terraform module is as easy as pushing a tag to the module's repository.
We recommend configuring VCS access when first setting up an organization, and you might need to add additional VCS providers later depending on how your organization grows.
Configuring a new VCS provider requires permission to manage VCS settings for the organization. (More about permissions.)
» Supported VCS Providers
Terraform Cloud supports the following VCS providers:
- GitHub.com
- GitHub.com (OAuth)
- GitHub Enterprise
- GitLab.com
- GitLab EE and CE
- Bitbucket Cloud
- Bitbucket Server
- Azure DevOps Server
- Azure DevOps Services
Use the links above to see details on configuring VCS access for each supported provider. If you use another VCS that is not supported, you can build an integration via the API-driven run workflow.
» How Terraform Cloud Uses VCS Access
Most workspaces in Terraform Cloud are associated with a VCS repository, which provides Terraform configurations for that workspace. To find out which repos are available, access their contents, and create webhooks, Terraform Cloud needs access to your VCS provider.
Although Terraform Cloud's API lets you create workspaces and push configurations to them without a VCS connection, the primary workflow expects every workspace to be backed by a repository.
To use configurations from VCS, Terraform Cloud needs to do several things:
- Access a list of repositories, to let you search for repos when creating new workspaces.
- Register webhooks with your VCS provider, to get notified of new commits to a chosen branch.
- Download the contents of a repository at a specific commit in order to run Terraform with that code.
Important: Terraform Cloud usually performs VCS actions using a designated VCS user account, but it has no other knowledge about your VCS's authorization controls and does not associate Terraform Cloud user accounts with VCS user accounts. This means Terraform Cloud's VCS user might have a different level of access to repositories than any given Terraform Cloud user. Keep this in mind when selecting a VCS user, as it may affect your security posture in one or both systems.
» Webhooks
Terraform Cloud uses webhooks to monitor new commits and pull requests.
- When someone adds new commits to a branch, any Terraform Cloud workspaces based on that branch will begin a Terraform run. Usually a user must inspect the plan output and approve an apply, but you can also enable automatic applies on a per-workspace basis. You can prevent automatic runs by locking a workspace.
- When someone submits a pull request/merge request to a branch, any Terraform Cloud workspaces based on that branch will perform a speculative plan with the contents of the request and links to the results on the PR's page. This helps you avoid merging PRs that cause plan failures.
» SSH Keys
For most supported VCS providers, Terraform Cloud does not need an SSH key — it can do everything it needs with the provider's API and an OAuth token. The exceptions are Azure DevOps Server and Bitbucket Server, which require an SSH key for downloading repository contents. The setup instructions for Azure DevOps Server and Bitbucket Server include this step.
For other VCS providers, most organizations will not need to add an SSH private key. However, if the organization repositories include Git submodules that can only be accessed via SSH, an SSH key can be added along with the OAuth credentials.
For VCS providers where adding an SSH private key is optional, SSH will only be used to clone Git submodules. All other Git operations will still use HTTPS.
If submodules will be cloned via SSH from a private VCS instance, SSH must be running on the standard port 22 on the VCS server.
To add an SSH key to a VCS connection, finish configuring OAuth in the organization settings, and then use the "add a private SSH key" link on the VCS Provider settings page to add a private key that has access to the submodule repositories. When setting up a workspace, if submodules are required, select "Include submodules on clone". More at Workspace settings.
» Multiple VCS Connections
If your infrastructure code is spread across multiple VCS providers, you can configure multiple VCS connections. You can choose which VCS connection to use whenever you create a new workspace.
» Configuring VCS Access
Terraform Cloud uses the OAuth protocol to authenticate with VCS providers.
Important: Even if you've used OAuth before, read the instructions carefully. Since Terraform Cloud's security model treats each organization as a separate OAuth application, we authenticate with OAuth's developer workflow, which is more complex than the standard user workflow.
The exact steps to authenticate are different for each VCS provider, but they follow this general order:
| On your VCS | On Terraform Cloud |
|---|---|
| Register your Terraform Cloud organization as a new app. Get ID and key. | |
| Tell Terraform Cloud how to reach VCS, and provide ID and key. Get callback URL. | |
| Provide callback URL. | |
| Request VCS access. | |
| Approve access request. |
For complete details, click the link for your VCS provider:
- GitHub
- GitHub Enterprise
- GitLab.com
- GitLab EE and CE
- Bitbucket Cloud
- Bitbucket Server
- Azure DevOps Server
- Azure DevOps Services
Note: Alternatively, you can skip the OAuth configuration process and authenticate with a personal access token. This requires using Terraform Cloud's API. For details, see the OAuth Clients API page.
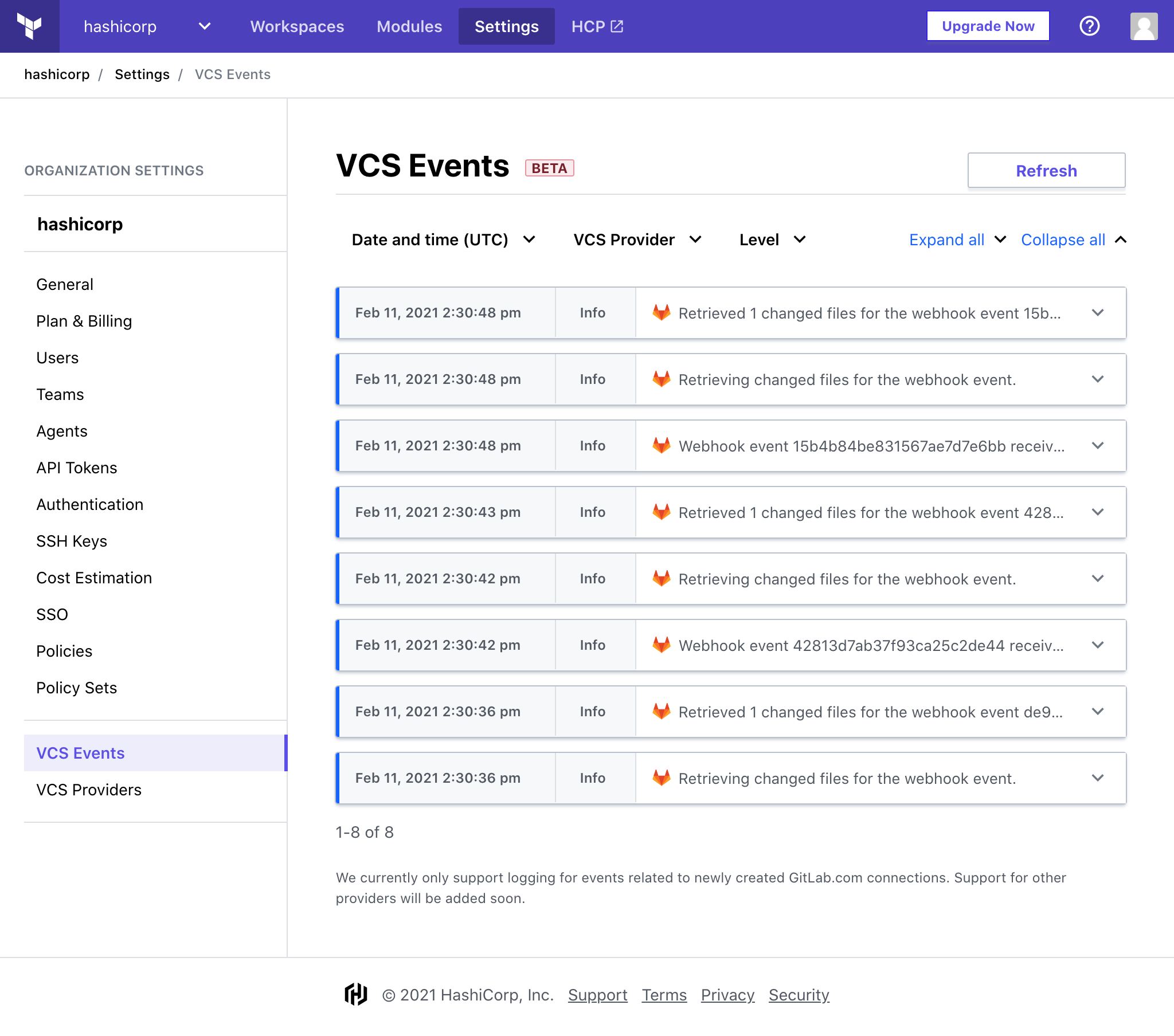
» Viewing events
Note: The VCS Event Viewer is still in beta as support is being added for additional VCS providers. Currently only GitLab.com connections established after December 2020 are supported.
VCS events describe changes within your organization for VCS-related actions, such as creating a new VCS provider (also called an OAuth Client), loading repositories while creating a new workspace, or processing incoming webhooks. Displayed events are limited to the past 10 days.
Viewing VCS events requires permission to manage VCS settings for the organization. (More about permissions.)